In the ever-evolving landscape of construction, the integration of cutting-edge technology has become imperative for future-proofing progress and ensuring the security of construction sites in the technological era. Traditional security measures are being augmented and, in some cases, replaced by sophisticated technologies that not only enhance safety but also streamline operations. One of the key advancements is the widespread adoption of smart surveillance systems. These systems utilize high-resolution cameras equipped with artificial intelligence AI capabilities, enabling real-time threat detection and proactive response mechanisms. This not only serves as a deterrent for potential intruders but also provides construction site managers with a comprehensive overview of the site’s security posture. Moreover, the implementation of drones has emerged as a game-changer in construction site security. Drones equipped with advanced cameras and sensors can efficiently patrol large areas, providing a bird’s-eye view of the entire site.

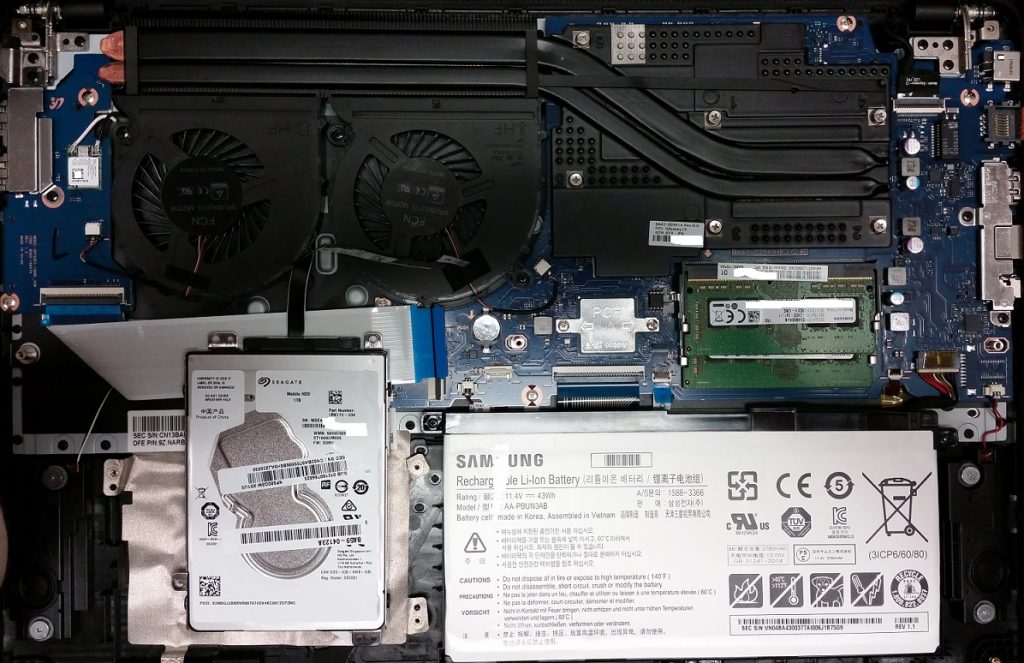
This aerial surveillance not only helps in monitoring for unauthorized access but also assists in assessing potential safety hazards. Drones equipped with thermal imaging can operate effectively during the night, ensuring 24/7 surveillance capabilities. The data collected by these drones can be seamlessly integrated with other security systems, creating a robust network that enhances the overall situational awareness of the construction site. Biometric access control is another technological frontier reshaping construction site security. Traditional methods such as key cards or PIN codes are being replaced by biometric solutions like fingerprint or facial recognition systems. These technologies not only improve access control but also prevent unauthorized individuals from gaining entry. Additionally, they provide a more accurate and secure means of tracking personnel movements within the construction site, ensuring that only authorized personnel have access to sensitive areas. The advent of the Internet of Things IoT has further revolutionized construction site security by enabling the interconnectivity of various devices. Smart sensors embedded in equipment, tools, and even personal protective equipment PPE can relay real-time data to a centralized monitoring system.
This data-driven approach allows for predictive maintenance, identifying potential security vulnerabilities before they escalate. For instance, if a construction tool is moved without proper authorization, the IoT sensors can trigger an immediate alert, enabling swift response to potential theft or sabotage and check this site https://www.securedbypremier.com/sacramento/security-trailers/construction/. As construction sites become more interconnected, cybersecurity has become an integral aspect of future-proofing progress. The integration of robust cybersecurity protocols ensures that the technological infrastructure supporting construction site security remains resilient against cyber threats. Firewalls, encryption, and regular security audits are essential components in safeguarding sensitive data and preventing unauthorized access to the interconnected systems. In conclusion, the future of construction site security lies in embracing the advancements of the technological era. By integrating smart surveillance, drones, biometric access control, and IoT-driven solutions, construction sites can not only enhance security but also improve operational efficiency. As the industry continues to evolve, staying ahead of the curve in technological adoption will be paramount to ensuring a secure and productive construction environment.